19 KiB
AWS Enumeration
Regions
A list of services by region is maintained by AWS There are global and regional services.
Watch out for the global and regional Security Token Service (STS) which provides temporary access to third party identities, since regional STS are also valid in other regions. Global STS are only valid in default regions.
In aws cli, Regions got
the cli argument --region
Identity Access Management (IAM)
Permissions are granted directly through IAM identities (IAM Principals) inside an AWS account or indirectly through groups and roles the principal (user or service) has joined.
aws iam list-users
Users can be put into groups instead of direct role assignment, to specify permissions for a collection of users.
aws iam list-groups
Roles can be assumed by other trusted users through policies. Assumed roles are
needed, so that aws support has access to some resources or external identity
Provider (idP) is connected to AWS SSO as a part of federated access. E.g. the
Role for support is AWSServiceRoleForSupport.
aws iam list-roles
Gaining access to important roles like maintenance opens the door to higher permissions.
Services use resources bound to the IAM inside the account. The scheme for
services is <servicename>amazonaws.com. Services, as trusted enitites, assume
roles to gain permissions.
A * represents every principal. Set the * to make an instance of a service
public through the Internet.
Identify an unknown accountname by using an access key
aws sts get-access-key-info --access-key <AKIAkey>
The IAM is not necessarily used by S3. AK/SK is sufficient for authentication and authorization.
- AWS got unique ID prefixes
- An AWS unqiue Account ID has a length of 12 digits.
- Longterm Access key ID, starts with
AKIA+ 20 chars - Secret access key (SK)
- Shortterm Session token,
ASIA+ sessionToken - AWS Organizations control accounts who joined
- Third party identity providers are supported
- IAM identity center of an organization allows provision of accounts from third parties through the AWS SSO
Root Accounts
Every AWS account has a single root account bound to an email address, which is also the username. This account has got the all privileges over the account. A root account has MFA disabled by default. It has all permissions except Organizational Service Control Policies.
The account is susceptible to an attack if the mail address is accessible but
MFA is not activated.
The email address of the root account, which is called MasterAccountEmail can
be found as member of an AWS Organization
aws organizations describe-organization
If the MFA is not set, it is an opportunity for a password reset attack when the account the vulnerable root belongs to is part of an AWS Organization.
If the email address is also linked to an Amazon retail account and it is shared between people, everyone has full root access.
Principal, Resource & Service Policies
Policies are an authorization measurement. After authentication of a user (or principal) policies of the account are checked if the request is allowed. A policy may also be attached to a resource or (in an organization) a service. Policy evaluation can be found in the AWS docs. There are resource and identity based policies.
aws iam get-policy --policy-arn <ARN>
Policy details consists of the following example
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": "s3:ListAllMyBuckets",
"Resource": "*"
}
]
}
Policy enforcement is done via the Effect keys and either has allow or
deny keys set in the JSON object. Deny is default.
The Action keyword contains a Service and an API keyword on on that service
in the scheme <servicename>:<APIKeyword>, e.g.
"Action":["ec2:Get*","ec2:Describe*", "s3:*"]. See the Service Authorization
Docs
The Resource key contains the ARN of the resource the policy is set for.
The Principal key is only set for resource policies and contains the
principal who is able to act on the resource. For example a * value allows
public access.
Operators can be used to set conditions using key value pairs inside policies
"Condition": {
"IPAddressIfExists": {"aws:SourceIp": ["xxx"] },
"StringEqualsIfExists": {"aws:sourceVpc": ["yyy"]}
}
Principals, resources and actions can also be excluded specifically through
NotPrincipal, NotResource and NotAction.
The following graph is taken from the documentation, it shows the evaluation logic inside an account
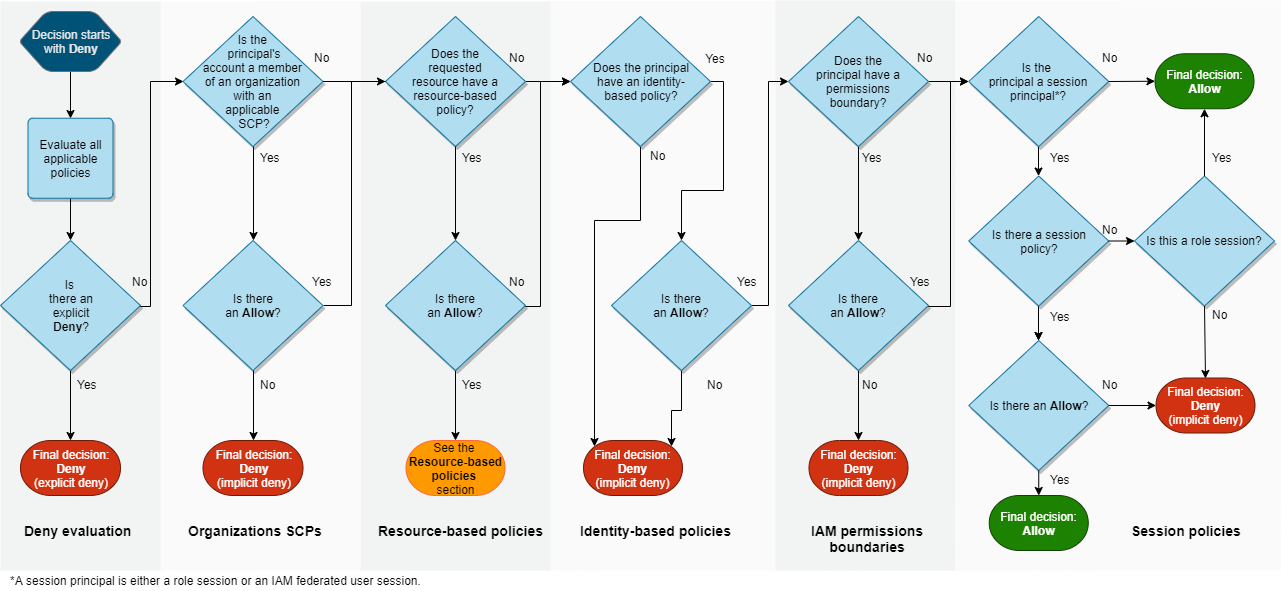
A principal can have multiple policies attached.
Policies like assume-role and switch-role can lead to the gain of roles
with higher permissions
A * inside a "Principal" value represents every principal. Set the * to
make an instance of a service public through the Internet like this following rule.
"Principal": {
"AWS": "*"
}
Administrator access policies can be queried to see who has elevated permissions.
aws iam get-policy --policy-arn arn:aws:iam::aws:policy/AdministratorAccess
aws iam get-policy-version --policy-arn arn:aws:iam::aws:policy/AdministratorAccess --version-id v1
The AdministratorAccess policy looks like this
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": "*",
"Resource": "*"
}
]
}
AWS Organizations
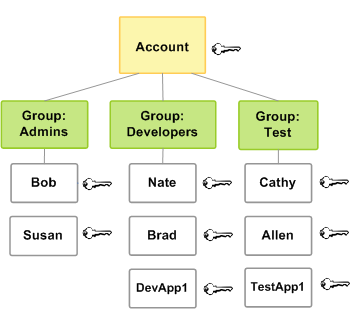
An organization is a tree structure, made out of a single root account and Organizational Units (UOs). UOs can have children UOs. AN UO may contain multiple AWS accounts. An AWS account can contain multiple user accounts.
An organization has IAM and SSO that also works with external identity Providers (idP). This is done through the AWS IAM Identity Center which is used to confiure roles and permissions.
Further, there is a management account inside any organization. It owns the
role "OrganizationAccountAccessRole". This account uses the policies/roles
mentioned in the User Policies which are assume-role and
switch-role on the cli tool and the management web-console to gain
administrative permissions over the UOs inside the organization.
By default the Service Control Policy (SCP) p-full-access it attached to
every account inside the organization. This SCP allows subscription to all AWS
services. An account can have 5 SCPs at max. Limiting SCPs do not apply to the
management account itself.
User Provisioning and Login
When using the cli command, the aws configuration and credentials are stored at ~/.aws
The
documentation
show how to setup the user login.
Add the credentials to the default plugin via
aws configure
Add credentials to a profile which is not default via
aws configure --profile PROFILENAME
Sanity test a profile through checking its existance via
aws iam list-users
aws s3 ls --profile PROFILENAME
Find account ID to an access key
aws sts get-access-key-info --access-key-id AKIAEXAMPLE
List the (current) user details
aws sts get-caller-identity
aws sts --profile <username> get-caller-identity
Find username to an access key
aws sts get-caller-identity --profile PROFILENAME
List EC2 instances of an account
aws ec2 describe-instances --output text --profile PROFILENAME
In another region
aws ec2 describe-instances --output text --region us-east-1 --profile PROFILENAME
Create a user via cloudshell.
aws iam create-user --user-name <username>
Add a user to a group via cloudshell.
aws iam add-user-to-group --user-name <username> --group-name <groupname>
List groups for a user using aws cli. GroupIds begin with AGPA.
aws iam list-groups-for-user --user-name padawan
Credentials
User credentials are called profiles on the webUI and console Password is used by the aws cli tool and queried APIs.
Create a user password via aws cli
aws iam create-login-profile --user <username> --password <password>
Change the password using the aws cli
aws iam update-login-profile --user <username> --password <password>
Take a look at the password policy via aws cli
aws iam get-account-password-policy
API Access Keys
Longterm, non-expiring Access key ID start with AKIA + 20 chars
List the access keys via aws cli.
aws iam list-access-keys
Create an access key via the aws cli.
aws iam create-access-key --user-name <username>
Disable, enable or delete an access key via the aws cli
aws iam update-access-key --access-key-id <AKIAkey>
aws iam update-access-key --access-key-id <AKIAkey>
aws iam delete-access-key --access-key-id <AKIAkey>
Shortterm Session Keys (STS)
Session keys are short term, they expire. A session key start
with ASIA.
These are generated by the Security Token Service.
Use aws cli to create a session token through STS.
aws sts get-session-token
Token can be applied to a user as a second factor. If the user is provided by another federated entity through idP the MFA needs to be provided through this solution.
List users with MFA enabled via aws cli.
aws iam list-virtual-mfa-devices
You can get the username of an account through the STS service using the access-key
aws sts get-access-key-info --access-key-id <AKIA-key>
The session token can be found via the cloudshell through the use of curl.
curl -H "X-aws-ec2-metadata-token: $AWS_CONTAINER_AUTHORIZATION_TOKEN" $AWS_CONTAINER_CREDENTIALS_FULL_URI
Assume Roles through STS
A an attack vector, a user can assume a role of higher privileges through the STS. This might happen through a policy bound to a group the user is a member of.
You need an ARN of the role you want to assume
arn:aws:iam::<ACCOUNT_ID>:role/<rolename>
A role session name from the CloudTrail logs is needed, somone who has got the role we want to assume.
Use aws cli to assume the role.
aws --profile <lowprivuser> sts assume-role --role-arn arn:aws:iam::<ACCOUNT_ID>:role/<rolename> --role-session-name <highprivuserthathastherole>
This result of this is to get the AccessKeyId, SecretAccessKey and SessionToken of the user to complete the three needed variables for aquiring the high privilege.
export AWS_SECRET_ACCESS_KEY=<HighPrivUserSK>
export AWS_ACCESS_KEY_ID=<HighPrivUserAK>
export AWS_SESSION_TOKEN=<SessionToken>
Check the current identity after setting the variables via aws cli.
aws sts get-caller-identity
Secrets
Use the secrets manager via
aws secretsmanager help
aws secretsmanager list-secrets
aws secretsmanager get-secret-value --secret-id <Name> --region <region>
Amazon Resource Name (ARN)
The ARN is a unique ID which identifies resources.
A Unique ID is create through the following scheme
arn:aws:<service>:<region>:<account_id>:<resource_type>/<resource_name>
Services
An action on an
API
of a service is structured like <servicename>:<APICall>.
Session tokens can also be created for services for temporary access of resources. This can be done through metadata service on an EC2 instance. The session token and AK/SK are also visible in the environment variables of AWS Lambda.
The session token can be found via the cloudshell through the use of curl.
curl -H "X-aws-ec2-metadata-token: $AWS_CONTAINER_AUTHORIZATION_TOKEN" $AWS_CONTAINER_CREDENTIALS_FULL_URI
Virtual Private Cloud (VPC)
Is a logic network segementation method using its own IP address range. Contains EC2 VMs and has an Internet gateway if needed. The gateway can be either just ingress, egress, or both. EC2 can use elastic IP addresses to provide Ingress. A Gateway Load Balancer can be used to do traffic inspection.
A VPC is part of the EC2 namespace ec2:CreateVPC
To connect to a VPC, it does not need to be exposed to the Internet. It is accessible through various connection services like Direct Connect or PrivateLink.
VPCs can have multiple subnets, they use host infrastructure components like DHCP, NTP and DNS provided by AWS.
NTP can be found under 169.254.169.123. The DNS resolver Route 53 can be
found under 169.254.169.253. Microsoft's KMS service can be at 169.254.169.250
and 169.254.169.251.
Metadata Service
The instance (Openstack) Metadata service can be found under 169.254.169.254.
It can be used
to gain information about the EC2 via a GET request to
http://169.254.169.254/latest/meta-data.
The task metadata service can be found at 169.254.170.2 and is used for the Elastic Container Service (ECS)
From inside a container curl can be used to get the credentials
curl 169.254.170.2$AWS_CONTAINER_CREDENTIALS_RELATIVE_URI
The instance metadata service has been used for information disclosure of security credentials before. Alexander Hose describes how to use the credentials through aws-cli.
[ec2-user ~] curl http://169.254.169.254/latest/meta-data/iam/security-credentials/
ec2S3FullAccess
[ec2-user ~] curl http://169.254.169.254/latest/meta-data/iam/security-credentials/ec2S3FullAccess
{
"Code": "Success",
"LastUpdated": "2022-10-01T15:19:43Z",
"Type": "AWS-HMAC",
"AccessKeyId": "ASIAMFKOAUSJ7EXAMPLE",
"SecretAccessKey": "UeEevJGByhEXAMPLEKEY",
"Token": "TQijaZw==",
"Expiration": "2022-10-01T21:44:45Z"
}
Use the credentials to configure aws-cli.
$ aws configure
AWS Access Key ID [None]: ASIAMFKOAUSJ7EXAMPLE
AWS Secret Access Key [None]: UeEevJGByhEXAMPLEKEYEXAMPLEKEY
Default region name [None]: us-east-2
Default output format [None]: json
Add the credentials to the AWS credentials file
[default]
aws_access_key_id = ASIAMFKOAUSJ7EXAMPLE
aws_secret_access_key = UeEevJGByhEXAMPLEKEYEXAMPLEKEY
aws_session_token = TQijaZw==
Simple Storage Service (S3)
S3 is an object storage without volume limits.
A nested directory structure in a bucket is possible, but pseudo file system for organizing files.
The names of buckets are unique and the namespace of buckets is global but they are stored regionally.
Versioning of files is possible. Files will not be overwritten by updated versions. Files are enrypted by default.
Methods of access control are as follows
S3 Policies
Useful permissions to an attack, set through a policy, are s3:GetObject and s3:PutObject.
There are identity based and resource based policies for s3 buckets. If global access or read is set, a resource based policy access to the objects is available in general of everyone, unauthenticated.
{
[...]
"Effect": "Allow",
"Principal": "*",
"Action": [
"s3:GetObject",
"s3:PutObject"
],
[...]
}
Check which policies are set
aws s3api get-bucket-policy-status --bucket <bucketname>
aws s3api get-bucket-ownership-controls --bucket <bucketname>
ACL
Existed since before AWS IAM. The ACL is generated for every bucket created. Resource owner gets full permissions. ACL can be extended through principals' canonical userID and services which are allowed or forbidden to access the bucket.
Attack vector: The group Any Authenticated AWS User can be set as permissions for a group of every
authenticated AWS user.
If the ACL is set to
Anyone, justcurlAuthenticatedUsers,s3cli with aws key
Scheme
The aws cli scheme for s3 is the following.
http://<bucketname>.s3.amazonaws.com/file.name
or
http://s3.amazonaws.com/BUCKETNAME/FILENAME.ext
Check Permissions of a bucket
Use a PUT method to see if the bucket may be writeable to upload a file via
curl -vvv -X PUT $BUCKET_URL --data "Test of write permissions"
List content of public bucket via
aws s3 ls s3://<bucketname>/ --no-sign-request
Download via curl, wget or s3 cli via
aws s3 cp s3://<bucketname>/foo_public.xml . --no-sign-request
Lambda
Execute a lambda function via aws cli.
aws lambda invoke \
--function-name arn:aws:lambda:<region>:<account_id>:function:<function_name> <arg1>
List policies
aws lambda get-policy \
--function-name arn:aws:lambda:<region>:<account_id>:function:<function_name> \
--query Policy \
--output text \
| jq .
CloudFront
CloudFront is a Content Delivery Network(CDN), which stores static data on Edge Locations, closer to the customer for performance improvements.
Geo-fences can be placed to access the content. Can also use authorization based requests,encryption of data is possible.
A Web Application Firewall (WAF) as well as Distributed Denial of Service (DDoS) prevention can be configured for CloudFront instances.
CloudFront Hosts
An "origin" of a CloudFront instance can be resources like EC2, ELBs or S3 buckets. Origin Access Identities (OAIs), which are resourced based policies for the resources or "origins" of a CloudFront instance, need to be set the owner. For an attack to take place, information about the DNS records of a domain is needed, to find probable CloudFront resources.
Use dig or drill or nslookup to list IP addresses of a (sub-)domain where assets are hosted, potentially. Do A reverse lookup to get the aws domains of the resources behind the IP addresses.
drill assets.example.com
drill <$IP_ADDRESS> -x
How to find a potentially interesting CloudFront assets domain
- Enumerate subdomains of a website
- Do some dorking with a search engine to list the content of a bucket behind an S3 subdomian
- Spider a website via wget or Linkfinder
- Search for certificate details